Data protection – More protection for Messenger users
Cryptography experts at Graz University of Technology want to achieve better protection of personal contacts on smartphones – and thus of sensitive data. Together with colleagues from TU Darmstadt, they have developed a process that makes address book data synchronization more secure when installing a messenger service. For this development, the research group was awarded second place at the German IT Security Prize, announced Graz University of Technology.
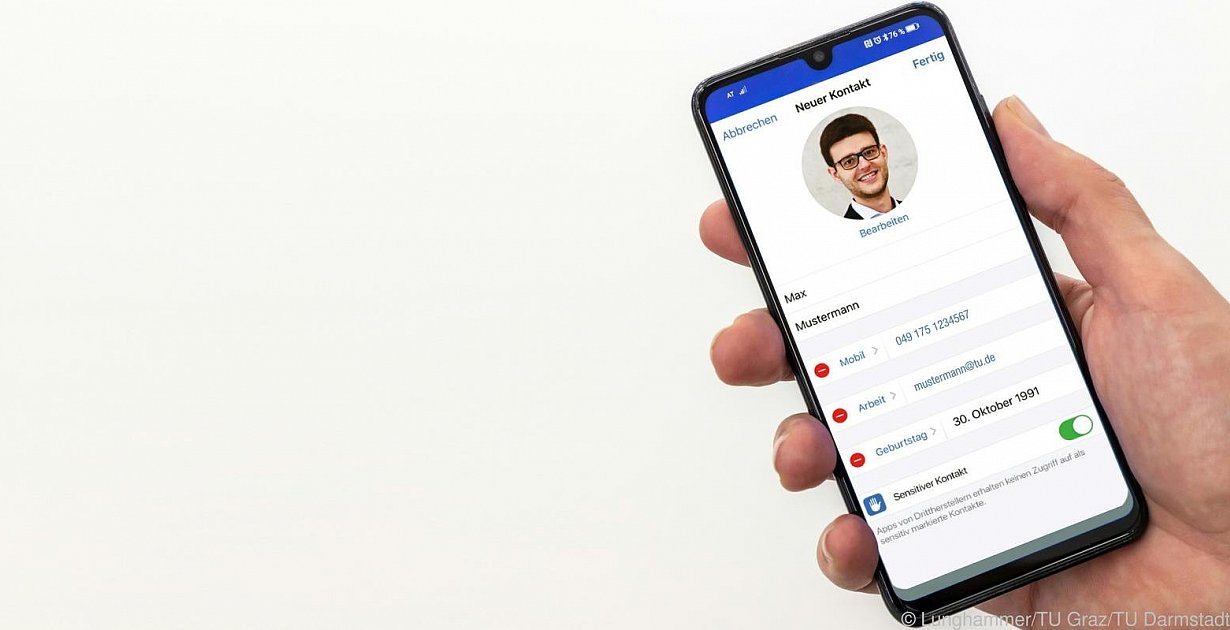
The installation of a messenger service on the smartphone, with which you can send voice messages, videos and pictures, is easy: As a user, you only have to quickly give the app permission to access the previous telephone address book. The service provider compares the telephone address books with its own contact database (overlap calculation) and updates them again and again through regular access. In this process, the entire address books are currently uploaded to the service provider’s servers. The common contacts between the service provider and the user are then determined using intersection calculations. This process can also lead to unwanted access to the contact information.
Hackers can collect large amounts of data
Many people are not even aware of the risk of invading privacy: malicious users or hackers can collect data on a large scale, as the researchers from Graz and Darmstadt have already collected. For example, behavior and contact patterns can be tracked from this. The “Mobile Contact Discovery” process also affects the privacy of those people who are stored in the phone book and who have not even installed the respective messenger and whose contact information is transmitted without being asked, as the Graz-based cybersecurity expert Christian Rechberger explained.
“There are currently no satisfactory solutions for a contact determination procedure for mobile messenger services. All previous options are either completely insecure or at least offer no protection worth mentioning,” said Rechberger, summarizing the challenge for developers. Rechberger teaches at the Institute for Applied Information Processing and Communication Technology at TU Graz and is also Area Manager for Data Security at the Graz Know-Center. Together with his institute colleague Daniel Kales and researchers from the TU Darmstadt, he has identified a new method of establishing contacts. It is intended to significantly limit or completely avoid dangers to privacy and critical scenarios such as spying on contacts, reselling data and evaluating sensitive relationships.
Security thanks to cryptographic protocols
For their “ContactGuard” project, the researchers have developed cryptographic protocols that are said to be many times more efficient and secure than previous approaches. Data encryption on both sides is intended to prevent sensitive data from the address books from being disclosed. In principle, the encrypted database of the service provider – thanks to a compression technique specially developed by the researchers – is sent to the user in a resource-saving manner and saved on the mobile phone. The address book entries are in turn encrypted with the secret key of the service provider, but without the user being able to see the secret key. Conversely, the service provider has no information about the address book entries of the users.
According to Rechberger, modern security chips in most smartphone models over the past seven years have increased the efficiency of cryptographic calculations many times over. When registering for the first time, the cryptographic calculations and data transfers could lead to a certain latency. “However, even in cellular networks for the synchronization of up to 1,000 contacts this is in the range of a few seconds,” said Rechberger. He hopes that the global data protection laws will be tightened in the medium term in the interests of greater privacy and that the providers of messenger services will be moved to act. The researchers want to use the prize money of 60,000 euros – in the spirit of the founder – to further develop the security software until it is ready for the market. (Apa)